Find and fix common issues fast
Identify hidden vulns that involve human interaction such as business logic flaws, identity management bypasses, and misconfigurations.
Tackle complex apps with ease
Test complex apps and features for payment processing, purchasing, file uploads, and elaborate user workflows.
Rely on battle-tested standards
Our methodology implements common testing standards such as OWASP, The Web Application Hacker Handbook, and SANS Top 25.
Use the right pentesters and tools for the task
We combine human-driven testing from a curated team of experts with scanners and custom tooling to get the high-impact results you want.
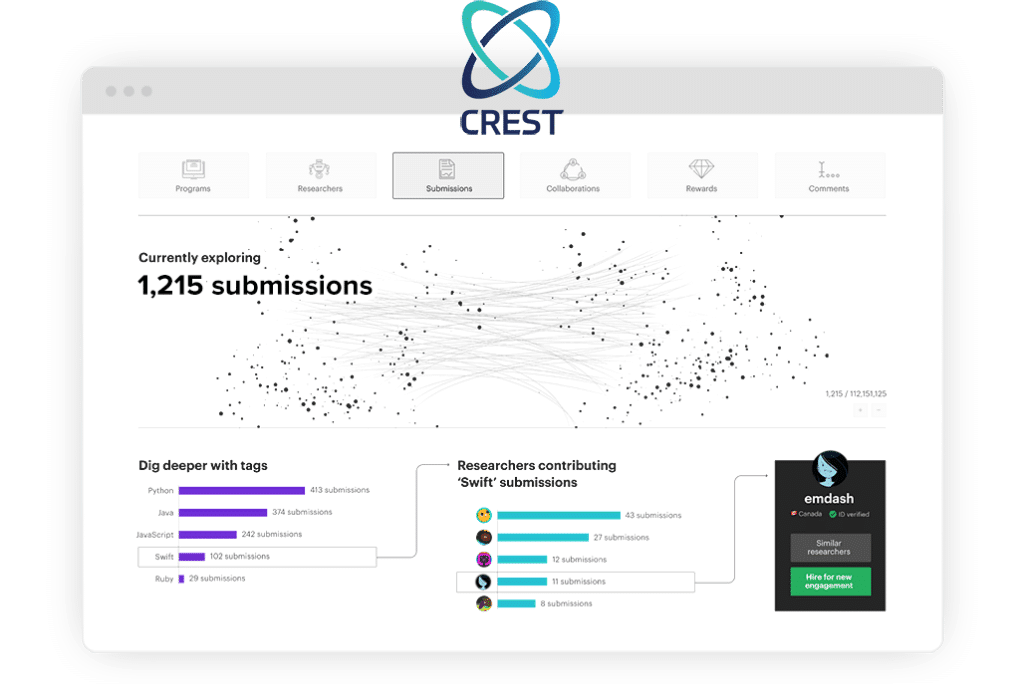
Curated Pentester Teams
Use a team your apps deserve
Other pen test providers rely on a cookie-cutter approach regardless of your specific assets, environment, or needs–virtually guaranteeing low-impact results. Instead, we use the power of CrowdMatchTM AI in our platform to curate qualified, motivated pentester teams for your precise requirements, boosting high-quality results over other methods.
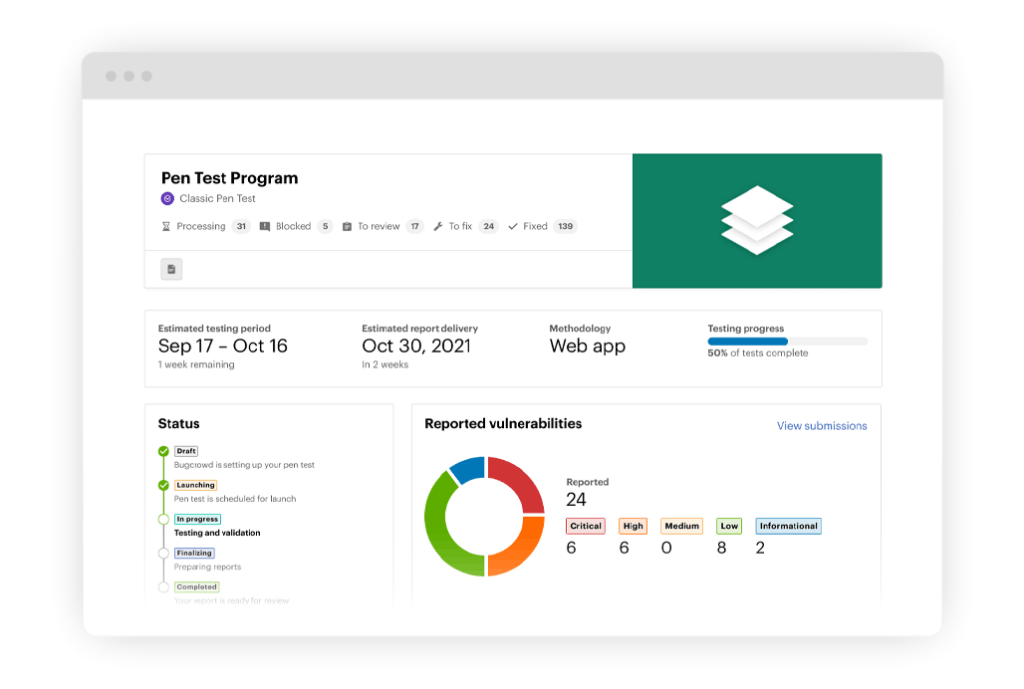
Penetration Test Dashboard
See results as they happen
Never be in the dark about your pen test results again. You can view prioritized findings, action items, analytics, and pentester progress 24/7 through the methodology checklist in a rich dashboard designed specifically for pen testing workflows. When ready, your final report (see sample for Standard pen test – Web App) is available for download from the same dashboard. Similar experiences for your other Bugcrowd solutions are just clicks away.
Pen test products
Optimized for today’s most demanding cybersecurity requirements
Shift Left: Flow Findings Directly Into Your SDLC

Compliance assurance as you need it





Get started with Bugcrowd
Attackers aren’t waiting, so why should you? See how Bugcrowd can quickly improve your security posture.


