Find and fix common issues fast
Find hidden vulns like misconfigurations, SQLi/CSRF opportunities, weak identity management, and insecure containers.
Go deep and wide
Our Cloud Configuration Reviews are thorough and deep, including reconnaissance, enumeration, scanning, and exploitation steps.
Rely on battle-tested standards
Our testing methodology follows industry-standard best practices from OWASP, PTES, and OSSTMM.
Use the right pentesters and tools for the task
We combine human-driven testing from a curated team of experts with scanners and custom tooling to get the high-impact results you want.
Curated pentester teams
Use a team your cloud deserves
Other pen test providers rely on a cookie-cutter approach regardless of your specific assets, environment, or needs–virtually guaranteeing low-impact results. Instead, we use the power of CrowdMatchTM AI on our platform to curate qualified, motivated pentester teams for your precise requirements, boosting high-quality results over other methods.
Pen test products
Optimized for today’s most demanding cybersecurity requirements
A Pen Test Offering for Everyone
Includes:
- Automated vulnerability assessment for PCI 6.6
- Basic report
Includes:
- Platform-generated report
- Expert, trusted pentesters
- Pen Test Dashboard
- Integration with SDLC
PLUS
Web Apps, Networks, Mobile Apps, APIs, Cloud, LLM Apps, Crypto, Binaries, IoT/OT/Hardware, and Onsite Testing
Everything in Standard +
- Customized report
- Support for special pentester requirements: Geolocation restrictions, special skill sets, etc.
- Retesting
- Internal Targets
Everything in Plus +
- Choice of continuous or on-demand testing
- Methodology-driven pen testing for coverage combined with bug bounty for discovery
Fast, scalable tests
Launch tests in days, not weeks. Findings flow directly into your dev and security processes for rapid remediation.
Higher impact results
Meet compliance goals and go beyond them when needed by incentivizing pentesters for results. (See Sample Report)
Deep configurability
Count on a pentester team built for your precise needs, and mix and match test types, methodologies, durations, and models.
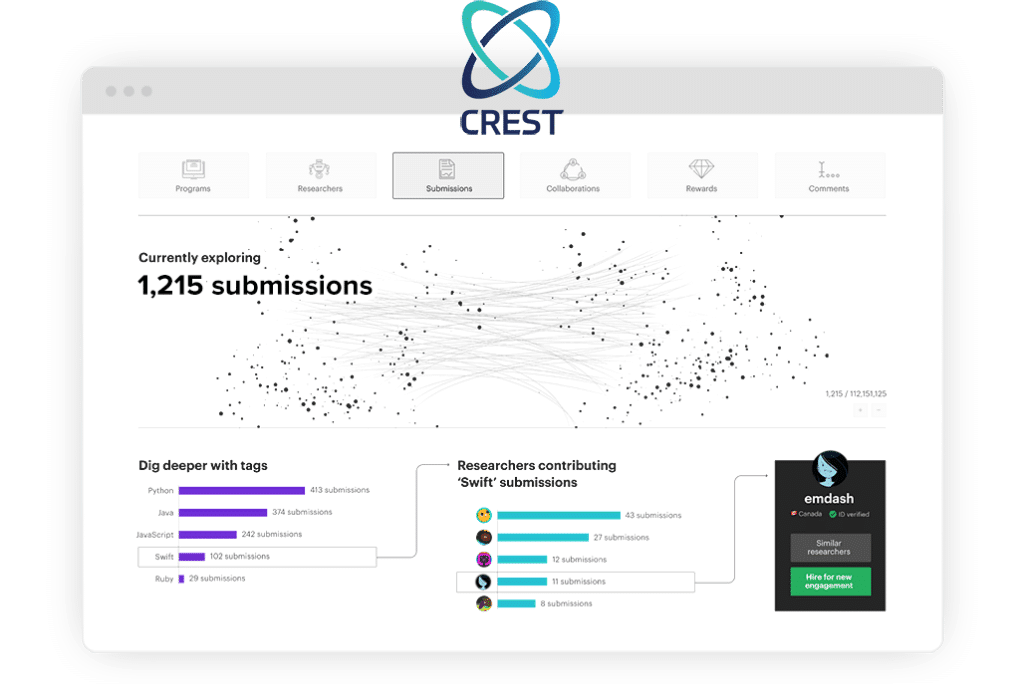
Real-time visibility
View findings and pentester progress through the methodology checklist in real time via the Bugcrowd Platform’s rich PTaaS Dashboard.
Shift Left: Flow findings directly into your SDLC

Compliance assurance as you need it





Get started with Bugcrowd
Attackers aren’t waiting, so why should you? See how Bugcrowd can quickly improve your security posture.


